Retrieve CloudHSM Credentials
You will receive multiple credentials that are used to authenticate your access to your CloudHSM. Retrieve these credentials, and store them safely. You will later need them when setting up the API providers.
- via Sales
- Online
Download the HSM Service Credentials
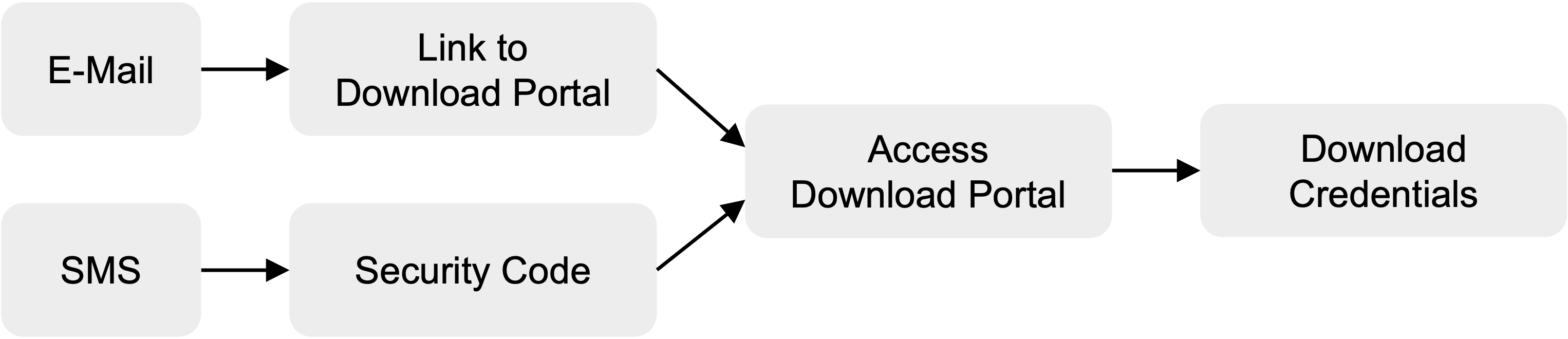
The provisioning of the HSM credentials must be performed by the privileged support user and include the following steps:
- Check your mailbox and look for one (or more) email with a SecureSafe link.
- Check your text messages on your mobile phone and look for one (ore more) password(s) (SecureCode).
- Use the password to download the HSM Service Credentials file(s) from SecureSafe.
Description of the Service Credentials
You will receive one or two sets of credentials depending on your subcription type:
- HSM Standard
- HSM with Multi-Tenant TSBaaS
- Standard
- Multi-Tenant TSBaaS
- Dedicated TSBaaS
You will receive 2 sets of credentials, in 2 separate emails:
- Service User credentials
- Technical User credentials
Both credentials apply to CloudHSM Sandbox (SBX), Economy (ECO), Certified (ECO-CC) and Platinum subscriptions.
1. What are the Service User Credentials?
The Service-User credentials are used to authenticate the CloudHSM subscriber on the service level. After successful authentication, the network gateway proxy permits the session to pass through to the HSM cluster.
The Service-User credential file contains the name and password to authenticate with reverse proxies.
Service User Name: ... # Reverse proxy Service-User name
Service User Password: ... # Reverse proxy Service-User password
HSM User Name: ... # Reference to HSM user/partition name
The Service-User credentials are also referred to as "Proxy-User"/"Proxy-Password".
2. What are the Technical User Credentials?
The Technical-User credentials are used when connecting for the first time with your HSM cluster Partition. This setup password will be disposed of and replaced with a user secret.
The user secret will never be revealed on display.
The Technical-User credentials are also referred to as "HSM-User"/"HSM-Password".
The Technical-User credential file contains the name and setup password to access the HSM Partition and PKCS#11 secret:
HSM User Name: ... # HSM user/partition name
HSM User Setup Password: ... # HSM user/partition initial password
PKCS#11 password : ... # if PKCS#11 API ordered
The Technical-User HSM Setup Password has a limited lifetime of 7 days:
- from the first usage, for CloudHSM Economy (ECO), Sandbox (SBX) and Platinum
- from the date of issuance, for CloudHSM Economy Certified (ECO-CC)
If you are not able to setup your application and connect to the HSM cluster within that time, please create a support ticket to renew the HSM Setup Password.
You will receive 1 single set of credentials with a JWT Token.
What is the JSON Web Token?
The JSON Web Token (JWT) serves as an authentication mechanism for CloudHSM subscribers within the multi-tenant TSBaaS environment. It enables secure communication with the CloudHSM Partition via the Transaction Security Broker (REST API).
The credential file contains a JSON Web Token to authenticate on Transaction Security Broker (TSB) and REST API.
- Details for REST API & Transaction Security Broker:
API-Endpoint: https://<service-url>.cloudshsm.com
JWT-TOKEN: ...
Documentation available at: https://<service-url>.cloudshsm.com/swagger-ui/index.html
- Select the 'Authorize' button and insert the JWT token if you wish to try out some commands on the Swagger-UI.
- You may also test connectivity using the following curl command:
curl -X GET 'https://sbx-rest-api.cloudshsm.com/v1/versionInfo' -H 'Authorization: Bearer <YOUR_JWT_TOKEN_HERE>
This authentication is based on mutual TLS (mTLS) and follows this process, in close cooperation between the Securosys Support Team and you.
Download the HSM Service Credentials via Cloud Console
- Log into Cloud Console.
- Go to MyServices page. Your service should appear in the list with the status Active.
- Click on the
Downloadbutton in the last column. A pop-up opens. - Copy/paste you 6-character PIN code. This was sent via email during the subscription.
- Click on the
Downloadbutton to retrieve the HSM Service credentials file.
The HSM Service credentials file will contain:
- Details for Native-API (JCE, PKCS#11, MS CNG)
HSM User Name: ... # HSM user/partition name
HSM User Setup Password: ... # HSM user/partition initial password
Service (Proxy) User Name: ... # Reverse proxy Service-User name
Service (Proxy) User Password: ... # Reverse proxy Service-User password
PKCS#11 password : ... # if PKCS#11 API ordered
- Details for REST API & Transaction Security Broker:
JWT-TOKEN for REST API & Transaction Security Broker: ...
Not all the HSM credentials provided are required for your service subscription.