Securosys KMIP Server
The Key Management Interoperability Protocol (KMIP) is an industry standard that enables systems and applications to manage cryptographic keys in a consistent, interoperable way across vendors and platforms.
Enterprise environments often include multiple systems that require encryption databases, storage arrays, backup solutions, and cloud services each with their own key management interfaces. KMIP provides a standardized protocol so these systems can communicate with any KMIP-compliant application, reducing complexity and preventing vendor lock-in.
Primary Use Cases
Centralized Key Management: Store all cryptographic keys in a secure, central location (such as an HSM), while applications access them through a standard protocol.
Enterprise Integration: Many enterprise platforms support KMIP natively, including VMware vSphere for VM encryption, database systems (Oracle TDE, MongoDB) for transparent data encryption, storage systems (NetApp, Dell EMC), and backup solutions (Veeam, Commvault).
Compliance and Security: Meet regulatory and security requirements through centralized key lifecycle management, audit trails, enforced rotation policies, and hardware-backed key storage.
Architecture
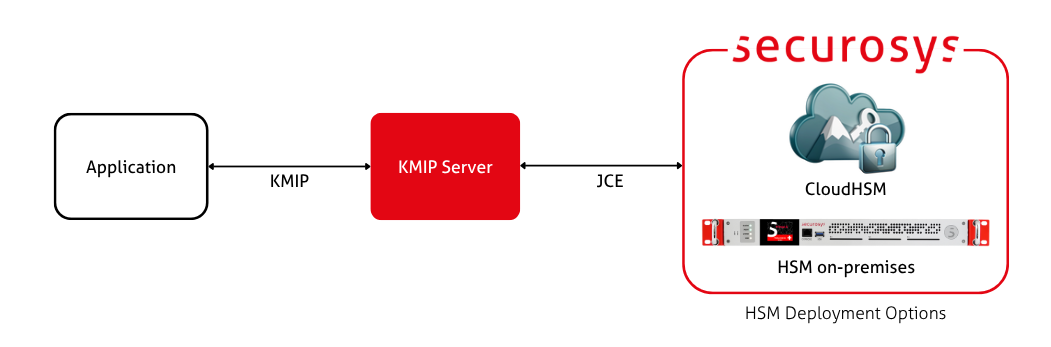
The Securosys KMIP Server acts as a bridge between KMIP clients (standard enterprise applications) and a Primus HSM or CloudHSM. It translates KMIP requests into JCE requests, which the HSM natively understands.
Cryptographic operations are executed by the HSM, while the KMIP Server manages protocol translation, client communication, and key lifecycle orchestration. This design ensures that the confidentiality and integrity protections of the HSM remain fully preserved.
Cryptographic keys are generated, stored, and managed within a FIPS 140-2 certified hardware environment. Additionally, the KMIP Server uses a database to cache non-secret metadata such as key identifiers and key attributes.
Deployment Models
1. Customer-Managed KMIP Server (default)
The KMIP Server is typically deployed on-premise within the customer’s trusted network:
- Full control over network boundaries, firewall rules, and connectivity.
- Suitable for highly regulated and isolated environments.
- Allows direct integration with existing enterprise PKI, IAM, and monitoring systems.
2. KMIP as a Service (KMIPaaS – available on request)
For customers who prefer a fully managed solution, Securosys can provide a hosted KMIP Server instance.
- Operated and maintained by Securosys with same SLA as describe in Service Level and Support Services
- Simplifies integration for cloud-centric or distributed architectures.
- Ensures the same security model and CloudHSM-backed key protection.
KMIPaaS deployments are not automatically included and must be discussed with Securosys to determine feasibility, requirements, and architecture.
Security Considerations
- Hardware Root of Trust: Cryptographic keys are generated and stored inside Securosys Primus HSMs.
- Mutual TLS (mTLS): All KMIP traffic between clients and the server is encrypted in transit and protected by mutual certificate-based authentication, preventing unauthorized access and man-in-the-middle attacks.
- HSM Communication Security: Communication between the KMIP Server and the HSM is conducted over a hardened, proprietary protocol designed for secure and tamper-resistant key operations.
- Audit Logging: All key lifecycle events and administrative actions are logged.
- Policy Enforcement: The KMIP Server centrally enforces key usage policies, expiration rules, and access permissions, ensuring consistent and auditable control over cryptographic resources.
What's Next?
- Check the prerequisites to run the KMIP Server.
- Jump to the installation guide to run the KMIP Server.