CyberVault KMS
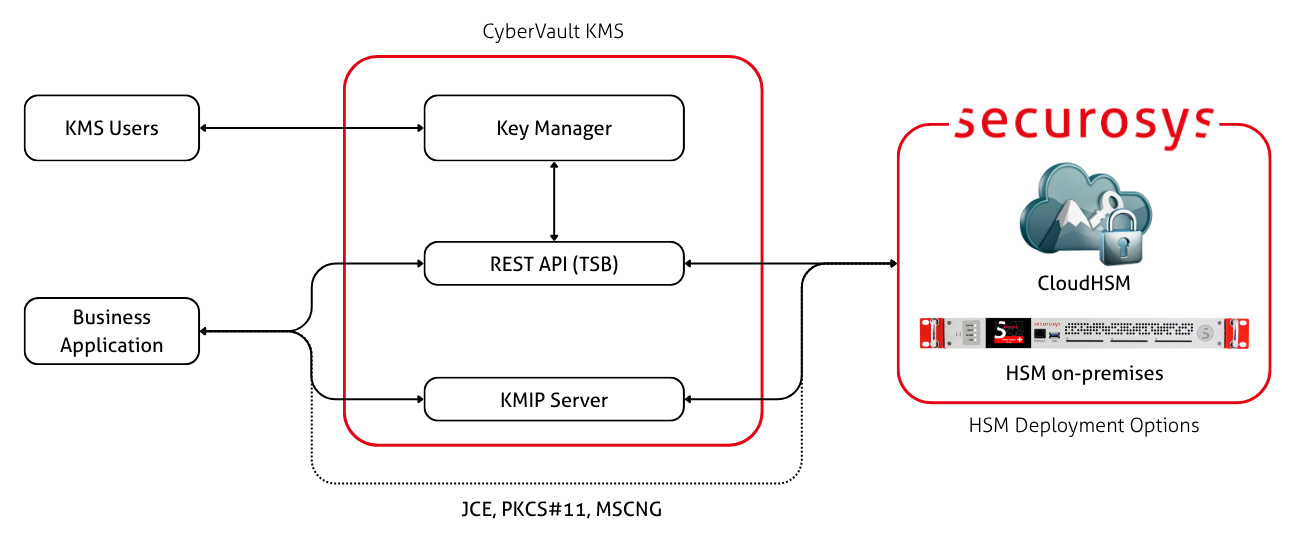
CyberVault KMS is the key management layer for Primus HSM and CloudHSM. It gives security and operations teams a web-based Key Manager UI, automation APIs, and KMIP connectivity for managing cryptographic keys, certificates, policies, approvals, and compliance from one simple web interface.
The key material itself remains protected inside certified Securosys HSMs. CyberVault KMS provides the control plane around the HSM Partitions: users can create and inspect keys, manage certificates, configure KMIP users, apply Smart Key Attribute policies, and monitor the cryptographic posture of their environment.
Features
CyberVault KMS brings the main key management workflows into a single operational view:
- Key and certificate lifecycle: Generate, import, rotate, inspect, attest, and delete cryptographic objects.
- SKA policy and approver management: Enforce multi-authorization of sensitive key operations using Smart Key Attributes.
- Application integration: Serve applications through the REST, KMIP, PKCS#11, MSCNG, and JCE while keeping keys inside the HSM boundary.
- Compliance visibility: Review audit activity, certificate health, key posture, and post-quantum readiness.
- Administrative delegation: Use role-based access control, multi-tenancy, and user management for operational separation.
Architecture
The CyberVault KMS is composed of four interdependent components. While each component has its own deployment and scaling considerations, they rely on one another to function. The HSM Cluster forms the cryptographic foundation, the REST API (TSB) is required before the Key Manager UI can operate, and the Key Manager UI must be running before the KMIP Server can be configured.
| Component | Description |
|---|---|
| Key Manager | Web-based management console for keys, certificates, policies, and compliance monitoring. Provides a dashboard with real-time HSM metrics, lifecycle actions, approval workflows, and audit visibility. |
| REST API (TSB) | Programmatic interface for automation and system integration. Supports fine-grained access control and audit logging. |
| KMIP Server | Key Management Interoperability Protocol (KMIP) endpoint for application integration. The Key Manager UI is needed to issue client credentials for the KMIP Server. |
| HSM Cluster | Certified hardware providing the cryptographic root of trust, redundancy, and scalability. Keys are generated and used within this secure boundary. |
Motivation
In modern cyber security architectures, cryptographic keys are the foundation of trust. Any encryption, any signature, and any security service built on cryptography is only as secure as the keys it uses.
As enterprises expand across hybrid and multi-cloud infrastructures, key lifecycle management becomes increasingly complex. A single missing control in key generation, storage, or rotation can compromise the entire security strategy of a company.
- Keys are the backbone of a company's operations, they perform decryption, signing, and authentication. Once exposed, encrypted data or digital identities are not secure and cannot be trusted.
- A key's lifecycle of generation distribution storage usage rotation revocation/destruction, is vulnerable to different attacks. Therefore, safety measures need to be taken for each step.
- Regulatory frameworks (e.g., PCI DSS, GDPR, ISO 27001, NIST SP 800-57, BSI TR-02102) mandate proper key control, logging, rotation, and hardware protection.
- The emergence of quantum computing threatens classical algorithms (RSA, ECC). Organizations must assess their cryptographic posture and plan migration to quantum-resistant algorithms.
- Without a strong KMS, key sprawl leads to operational vulnerabilities, compliance risk, and loss of sovereignty in cloud environments.
- A well-designed KMS enforces policies, ensures consistent governance, and provides auditable control over every key operation.
Benefits
| Area | Description |
|---|---|
| Centralized Control | Unified key, certificate, and secret management through one interface. |
| Hardware Trust Anchor | All keys reside within Securosys Primus HSMs - never exposed in software. |
| Approval Workflows | Enforced via Smart Key Attributes (SKA), reducing insider risk and supporting dual control. |
| Compliance & Audit | Continuous audit logging and compliance assessment against NIST SP 800-57, ISO 27001, and BSI TR-02102 requirements. |
| Flexible Deployment | Available on-premise, hybrid, or in the cloud, with integration into major IAM systems (OAuth 2.0, LDAP, AD). |
| High Availability | HSM clustering provides redundancy and fault-tolerance for mission-critical applications. |
| Multi-Tenancy | Partition-based isolation with per-user credentials and role-based delegation for multi-organization environments. |
Next Steps
The rest of this documentation section is dedicated to the Key Manager UI. The Key Manager UI is the administrative, operational, and monitoring layer of the CyberVault KMS.
- Explore the user-facing feature set of the Key Manager UI.
- Learn more about the architecture of CyberVault KMS and how it is deployed.
To deploy the full CyberVault KMS stack, follow the component guides in the following recommended order:
- HSM cluster: The cryptographic foundation. All other components depend on a running HSM cluster.
- REST API (TSB): Must be deployed before the Key Manager UI, as the UI uses the TSB to communicate with the HSM. Other applications can also use the REST API to interact with the HSM.
- Key Manager UI: The main web interface of CyberVault KMS.
- KMIP Server: Requires the Key Manager UI, as TLS client credentials for KMIP are issued through it. Any KMIP-compliant application can use it to interact with the HSM.