Wallet Key Derivation
Many crypto currency wallets have a single seed from which an entire tree of sub-wallets is derived. This page provides an overview of the key derivation algorithms that power these wallets. Primus HSM supports popular schemes such as SLIP-10 and BIP-32.
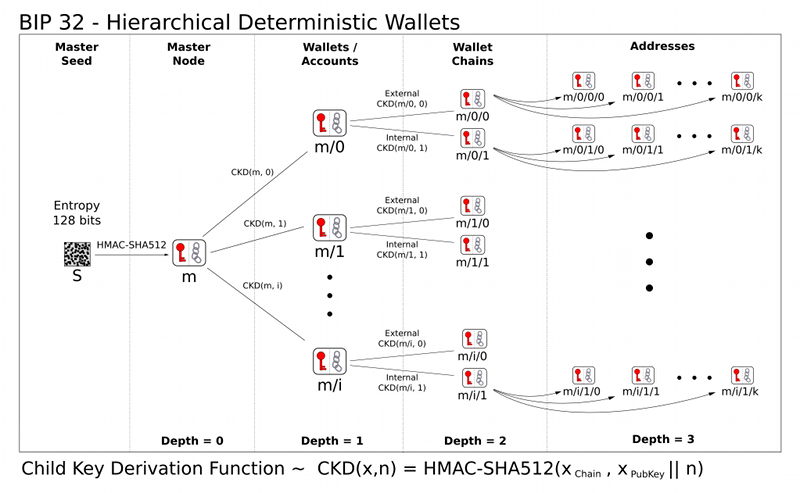
Hierarchical Deterministic Wallets
Many crypto currencies have the concept of "hierarchical deterministic wallets (HD wallets)". The idea is to have a single seed from which a root key pair is derived (also called master key pair). From that root key pair, a tree of child key pairs can be derived. Every child key pair corresponds to a wallet which can send and receive crypto currency funds.
This has multiple advantages:
- Users only need to back up a single seed phrase.
- Users can organize their wallet into sub-accounts. Apart from keeping funds logically separate, this also improves privacy, since transactions are spread across multiple, seemingly unrelated accounts.
- It enables the cryptographic principle of key separation.
Bitcoin has defined HD wallets in BIP-32 (Bitcoin Improvement Proposal 32) using curve secp256k1. Later, SLIP-10 (SatoshiLabs Improvement Proposal 10) generalized the concept from BIP-32 to support more curves: secp256k1, NIST P-256, ed25519, and curve25519. Therefore, for simplicity, we often only talk about SLIP-10.
Master Key Generation
SLIP-10 and BIP-32 define how to generate an elliptic curve master key pair from a binary seed value. This master key generation is supported by Primus HSM. Sometimes, this process is called "seeding".
The binary seed value may have been derived from a BIP-39 mnemonic phrase. This is outside of the scope of Primus HSM.
Child Key Derivation
SLIP-10 and BIP-32 also define how to generate child keys from the master key.
Child keys can be identified by their derivation paths,
as originally proposed by BIP-44.
An example derivation path is m/44'/0'/0'/0/0.
The derivation path defines the path from the root of the derivation tree to the child key that is to be derived.
 Source: https://github.com/bitcoin/bips/blob/master/bip-0032.mediawiki
Source: https://github.com/bitcoin/bips/blob/master/bip-0032.mediawiki
In order to derive another key from a base key in Primus HSM, the derive key attribute
must be set to true on the base key.
This attribute allows using the base key to derive child keys.
Additionally, the bip32or the slip10 key attribute should be set (to select the derivation algorithm).
In Primus HSM, derived child keys can be:
- Persisted: Created once and stored on disk. Fill up storage, but are immediately accessible.
- Temporary: Are re-computated every time they are used. Session objects, not stored on disk.
Background: Key Derivation
Key derivation involves generating new cryptographic keys from existing ones. This is useful if you are starting from a single root key and want to obtain several (sub-) keys that are cryptographically separate from each other.
Key derivation is possible with both symmetric keys (with algorithms like HKDF) and asymmetric keys (elliptic curves, but not RSA). For example, the TLS 1.3 key schedule makes heavy use of HKDF. This section is about key derivation with EC/ED keys. These are common in crypto currency use cases, such as SLIP-10.
Firmware Support
SLIP-10 is supported on HSM firmware version v3.0 and above. BIP-32 was supported on v2.7 and above, but was removed in v3.0 in favor of SLIP-10 with curve secp256k1.
API Support
SLIP-10 is supported on the following API providers: